Questo articolo è disponibile anche in lingua italiana al seguente link: Microsoft Local Administrator Password Solution: implementazione e gestione | WindowServer.it
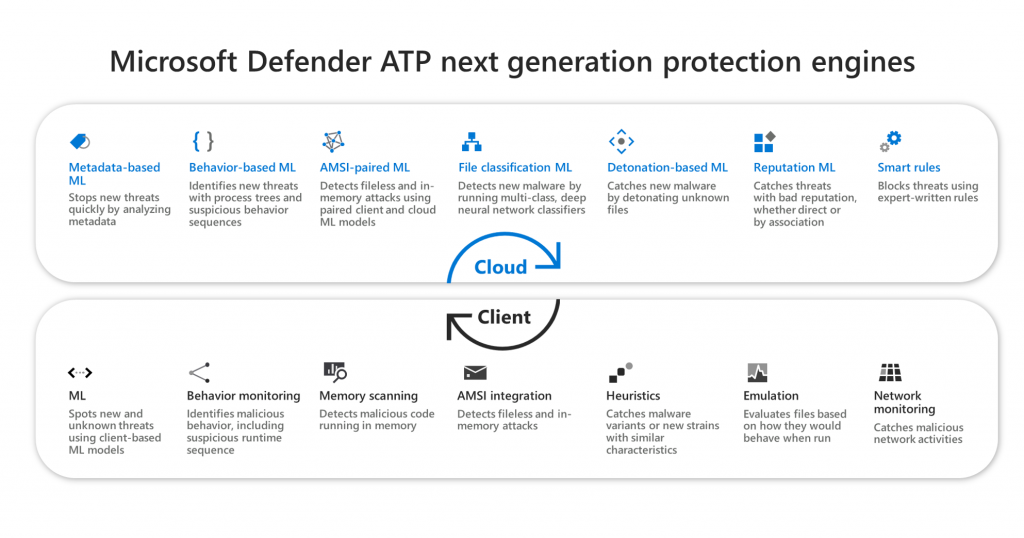
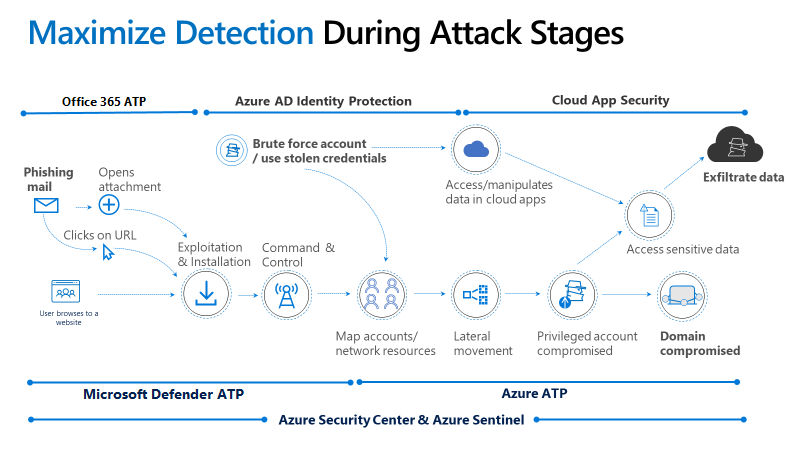
Computer security goes through every single detail and clients are perhaps the aspect on which to focus the major forces, because they are more exposed and because they are used by users who ignore the concept of security in particular what could be dangerous or not. Coupled with this is the fact that not all companies have XDR tools, such as Microsoft Defender ATP, or systems to protect file servers, e-mail and everything else used in the corporate ecosystem.
LAPS
Local Administrator Password Solution is a free product, made available to Microsoft, which is used to generate a unique password for each single machine within Active Directory and protected by ACLs that guarantee access only to authorized users.
The reason for adopting this system is simple: the most advanced ransomware are able to steal the credentials of administrative users by attacking the Windows Credentials Manager, leading the malware to attack other computers around the network, up to the servers. By eliminating the domain administrative credentials from the clients, you avoid that, even in the event of an attack, a valid user would be taken only for that machine.
Install
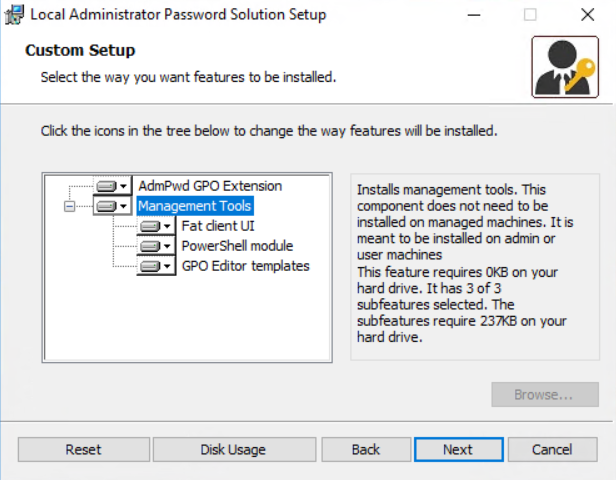
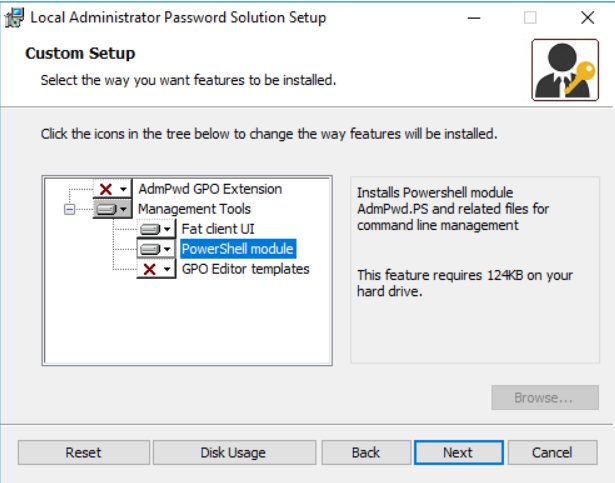
The first thing to do is to install the LAPS client inside a machine that also has the Active Directory PowerShell cmdlets, or inside one of the Domain Controllers.

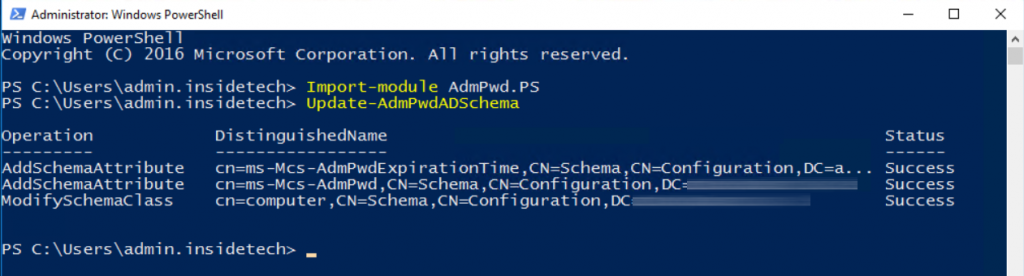
Once the installation is complete, run the following commands with an account with the privileges to modify the AD Schema: Import-module AdmPwd.PS and Update-AdmPwdADSchema
The computers must be able to update the password by themselves when the period set via GPO expires, so you need to run the following PowerShell command: Set-AdmPwdComputerSelfPermission -OrgUnit
NB: the operation must be performed for all OUs where there are clients that you intend to manage with LAPS.
As mentioned previously, the advantage of this solution lies in the granularity of being able to manage access to passwords via ACL and this translates into assigning the relative permissions to an Active Directory group in order to view and change passwords. To do this you need to run the following commands:
- Set-AdmPwdReadPasswordPermission -OrgUnit -AllowedPrincipals “AD Group Name”
- Set-AdmPwdResetPasswordPermission -OrgUnit -AllowedPrincipals “AD Group Name”
Group Policy
After enabling the Active Directory part, you need to distribute the settings to clients via GPO and to do this you need to import the .admx file located in the %SystemRoot%\PolicyDefinitions to the folder SYSVOL\PolicyDefinitions.
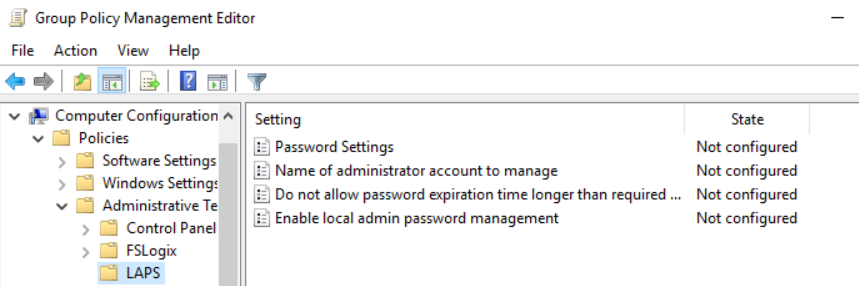
The policies to activate are the following:
- Enable local admin password management: Enabled
- Do not allow password expiration time longer than required by policy: Enabled
- Password Settings
Deployment
Distribution must be done on each client that you intend to manage: via GPO, via WSUS, via Microsoft Endpoint Configuration Manager, via Microsoft Endpoint Manager…..there are many ways to do it, or via script with the command msiexec /i “LAPS.msi” /q .
Password Recovery
The login password can be recovered in three different ways:
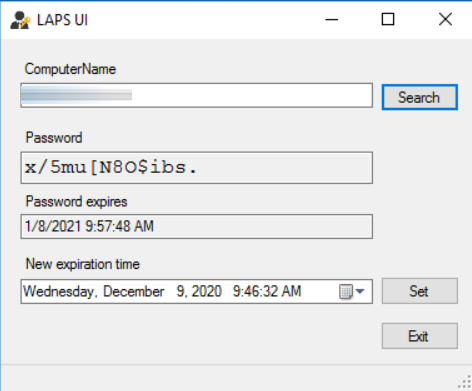
- LAPS UI
- PowerShell (Get-AdmPwdPassword “Computer Name ” | Out-Gridview)
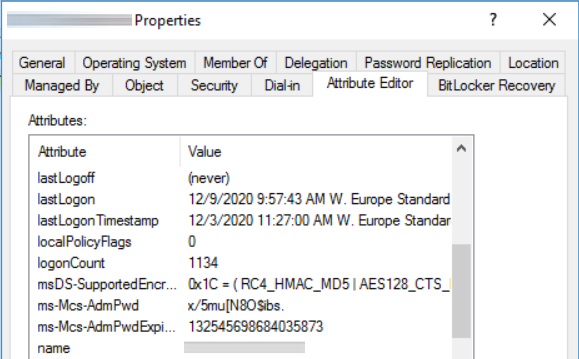
- Active Directory snap-in
As mentioned above, only if the user is enabled to manage the credentials of that specific OU will he be able to view its content. In the case of LAPS UI it is sufficient to enter the device name and perform the search.
In the case of Active Directory, you need to open the snap-in of the machine in question to view the password attribute under ms-Mcs-AdmPwd
Conclusions
Microsoft Local Administrator Password Solution is certainly a great tool that every company should implement to increase the internal security of their corporate infrastructure. The simply usage, and the point that it’s free, should be an accelerator to deploy now the solution! In the case of complex infrastructures, it is recommended to first read the documentation to perform a correct sizing ( LAPS and AD sizing considerations | Microsoft Docs ).
Get Started
Download Local Administrator Password Solution (LAPS) from Official Microsoft Download Center
#DBS